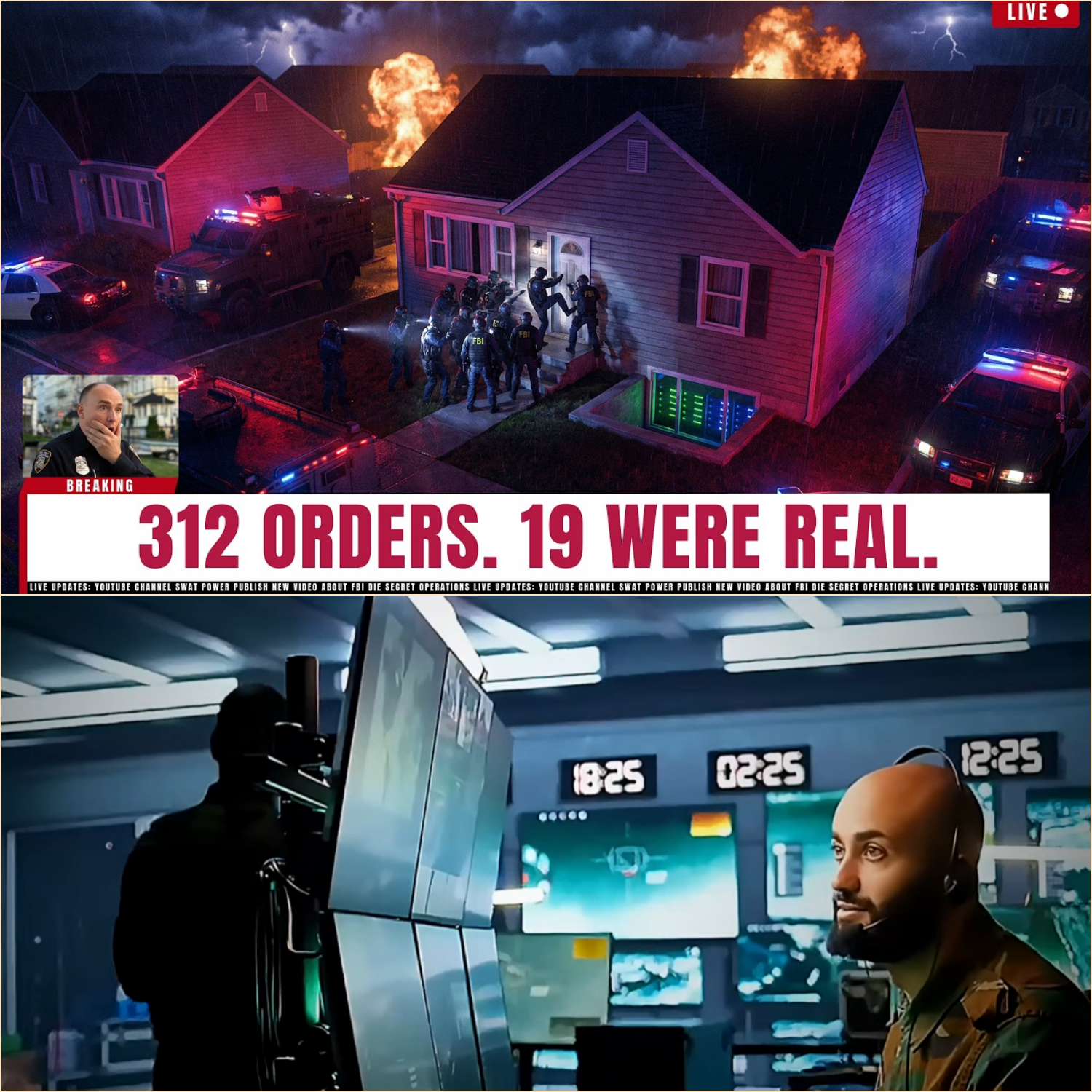
FBI CYBER UNIT TRACES Dark Web Hitman Service — 312 Orders, 19 Were Real
.
.
.
🇺🇸 PART 2 — FBI Uncovers the Hidden Kill Network Behind “Final Order”
The servers seized from the basement on Kelner Road did not simply contain names, payment records, and encrypted conversations. What FBI forensic analysts discovered during the weeks that followed would transform Operation Closed Circuit from a cybercrime investigation into something far more disturbing — a sprawling underground ecosystem where anonymous violence could be purchased, outsourced, and executed with terrifying efficiency.
Inside the mirrored hard drives recovered from Marcus Drier’s basement, agents found traces of a second system hidden beneath Final Order’s visible marketplace. It was not accessible through the platform’s public login portal. It did not appear in ordinary user navigation. And according to investigators, only a select group of trusted users ever knew it existed.
The internal codename was “Black Tier.”
Unlike the public-facing side of Final Order — where most users were merely scammed out of cryptocurrency payments — Black Tier allegedly functioned as the platform’s real operational core. Here, the rules changed. Customers who demonstrated persistence, financial capability, and emotional commitment to violence were quietly filtered upward into a private referral structure populated by intermediaries, recruiters, and suspected contract perpetrators.
Federal investigators would later describe it as “a criminal marketplace hidden inside another criminal marketplace.”
The realization stunned even veteran cybercrime analysts.
For years, dark web murder-for-hire sites had largely been dismissed as elaborate fraud schemes designed to exploit desperate, angry, or unstable people. Most never progressed beyond stolen cryptocurrency and fake promises. But Final Order blurred the line between scam and organized violence in ways law enforcement had never fully encountered before.
And now, federal agents understood why.
The scam was never a flaw in the business model.
It was the business model.
By allowing hundreds of fake contracts to circulate through the platform, operators could identify the users most willing to continue escalating payments, communication, and commitment. Those individuals became candidates for Black Tier access.
In essence, Final Order operated like a predator testing prey.
Most users vanished after losing money. Some became frightened and disappeared. But the few who persisted — those who repeatedly contacted administrators, requested updates, increased payment offers, or demonstrated obsession with specific targets — were quietly moved deeper into the system.
That was where real violence began.
According to sealed investigative summaries reviewed by federal prosecutors, Black Tier users received access to additional encrypted communication channels separate from the main platform. Unlike standard users, they could negotiate directly with intermediaries tied to actual perpetrators.
Those communications were heavily compartmentalized.
Marcus Drier’s servers contained fragments of metadata, partial timestamps, and encrypted routing information, but the actual message contents had been wiped using automated deletion protocols triggered every 72 hours. Even so, investigators recovered enough remnants to piece together a chilling operational structure.
There were brokers.
There were recruiters.
And somewhere beyond them were individuals willing to carry out attacks for cryptocurrency payments routed through untraceable channels.
What investigators still could not determine was whether those perpetrators operated independently or belonged to organized criminal cells. The evidence pointed in multiple directions simultaneously.
Some attacks appeared amateur and impulsive.
Others displayed startling precision.
One attempted homicide in Arizona involved a carefully staged roadside ambush executed with military-style discipline. Another case in North Carolina involved a manipulated vehicle collision initially ruled accidental by local police before federal investigators reopened the file months later.
The patterns varied.
The professionalism varied.
But the money trail always returned to Final Order.
As Operation Closed Circuit expanded, analysts from the FBI Cyber Division, Europol’s EC3 unit, and multiple intelligence agencies began reconstructing timelines from recovered logs. What emerged was a disturbing portrait of modern criminal outsourcing — violence fragmented across continents, encrypted networks, and layers of anonymity designed to ensure nobody ever saw the entire machine.
In Kraków, Poland, investigators searching Arena Morozova’s apartment uncovered handwritten notebooks filled with cryptic alphanumeric strings, wallet references, and abbreviated geographic markers. At first glance, the notes appeared meaningless. But after cross-referencing them against blockchain intelligence and server timestamps, analysts concluded the notebooks likely tracked commission structures tied to referred customers and fulfilled contracts.
One recurring notation appeared beside multiple entries:
“Verified.”
Federal prosecutors now believe the word indicated that a violent act had actually occurred.
That discovery changed the tone of the entire investigation.
This was no longer simply about online solicitation.
People had died.
And investigators increasingly feared the true number of violent incidents connected to Final Order might exceed the confirmed 19 cases already identified.
The challenge was scale.
The FBI had recovered 312 customer profiles. But not all users submitted real target information. Some used aliases. Others uploaded incomplete data or intentionally vague descriptions. Many communications referenced victims only by initials or nicknames.
Agents faced an immense digital puzzle scattered across thousands of encrypted records.
In one conference room inside the FBI’s Washington Field Office, analysts reportedly covered entire walls with printed timelines connecting cryptocurrency transfers, platform logins, unsolved crimes, burner wallets, and travel records. Colored strings linked photographs of suspects, victims, and digital identifiers in a sprawling map of modern clandestine violence.
And everywhere investigators looked, the same reality emerged:
The internet had made murder scalable.
A decade earlier, arranging violence required physical criminal networks, trusted intermediaries, or direct underworld connections. Final Order changed that equation. Now, an isolated individual with enough money and enough resentment could enter a hidden marketplace from a bedroom laptop and attempt to outsource violence across state lines without ever meeting another conspirator face-to-face.
That democratization of criminal access terrified investigators.
One FBI behavioral analyst involved in the case reportedly described Final Order as “Uber for violent grievance.”
The phrase circulated quietly through federal briefings.
Meanwhile, the human stories behind the platform continued unfolding with devastating clarity.
In Portland, Oregon, investigators interviewed the tenant whose car had been destroyed after property manager Diane Hargrove allegedly submitted his information through Final Order. He described months of fear following the arson attack — waking at night to unfamiliar sounds, checking mirrors while driving, moving between temporary housing locations because he believed someone might return to finish the job.
In Phoenix, the former business partner attacked outside his home during a financial dispute required reconstructive surgery after the assault shattered bones around his eye socket. Until the FBI contacted him, he reportedly believed the attack had been random street violence.
Then there was the Norfolk case.
Rachel Engel’s family learned through federal investigators that her death had not been spontaneous violence, but an arranged killing allegedly initiated by someone she once trusted. Court filings later revealed Derek Engel had searched Final Order forums repeatedly over several weeks before submitting payment.
The searches included phrases investigators described as “premeditated escalation behavior.”
“How long before confirmation?”
“What if target changes routine?”
“Need certainty.”
Those messages now sit inside federal evidence archives alongside transaction records and encrypted logs recovered from the platform.
For investigators working the case, the emotional toll mounted rapidly.
Unlike traditional organized crime investigations, Operation Closed Circuit forced agents to confront a uniquely modern horror: ordinary people transforming private resentment into anonymous outsourced brutality through digital infrastructure designed originally for privacy and free communication.
The same technologies protecting dissidents, journalists, and activists worldwide had also created spaces where violent conspiracies could flourish invisibly.
That contradiction became central to internal federal debates following the takedown.
Some officials argued for expanded monitoring powers targeting anonymity networks like Tor. Others warned against overreach, noting the platform itself had only been identified because of operational mistakes made by its operators, not because the underlying technology had failed.
Privacy advocates closely watched the case as legal battles intensified.
Marcus Drier’s defense attorneys moved aggressively to suppress key evidence, arguing the FBI’s monitoring of Tor relay nodes violated constitutional protections against unreasonable searches. Prosecutors countered that the exposed IP address was transmitted voluntarily during routine network operations and lawfully captured under existing court authorization.
Cybersecurity experts understood the implications immediately.
If the court sided with Drier’s defense, portions of the investigation could face legal jeopardy.
If prosecutors prevailed, federal agencies might gain broader precedent for future dark web investigations.
The courtroom battle promised to shape cybercrime enforcement for years to come.
But outside the legal war, another danger remained unresolved.
The unidentified perpetrators.
Despite recovering customer databases, payment logs, and internal communications, investigators still had almost no direct evidence identifying the individuals who physically carried out the 19 violent attacks.
That missing layer haunted the task force.
Some analysts believed the perpetrators operated as freelance criminals recruited opportunistically through encrypted referrals. Others suspected deeper organized crime connections stretching across Eastern Europe and North America.
A third theory disturbed investigators most of all.
What if the perpetrators were not professionals at all?
What if some attacks had been committed by ordinary individuals radicalized through the same online ecosystems that facilitated the contracts themselves?
The possibility introduced an even darker dimension to the investigation.
Because if true, Final Order was not merely connecting customers with killers.
It was cultivating them.
Investigators revisiting platform communications noticed recurring language encouraging emotional escalation. Users expressing hesitation were reassured. Users displaying anger were rewarded with faster responses. Repeat customers received privileged treatment and referral opportunities.
Psychological manipulation appeared embedded directly into the platform’s design.
The operators understood their audience intimately.
Loneliness.
Bitterness.
Financial desperation.
Romantic obsession.
Professional humiliation.
Family disputes.
The platform fed upon private grievances and transformed them into monetized criminal intent.
And the demand was staggering.
Three hundred twelve individuals placed murder requests through Final Order over less than three years. Federal analysts privately admitted the number likely represented only a fraction of broader dark web demand for anonymous violence services.
New marketplaces were already appearing before Final Order’s servers even finished processing inside FBI evidence facilities.
Clone sites emerged across encrypted forums within weeks of the takedown. Some falsely claimed ties to Final Order itself. Others used the investigation as marketing material, promising improved operational security and “guaranteed fulfillment.”
The cycle was already beginning again.
Federal agencies understood the uncomfortable truth: shutting down one platform did not eliminate the demand driving it.
As media coverage intensified, lawmakers demanded hearings on cryptocurrency regulation, dark web marketplaces, and cyber-enabled violent crime. Some officials pushed for expanded oversight of privacy-focused cryptocurrencies like Monero, arguing the technology had become indispensable infrastructure for transnational criminal operations.
Cryptocurrency advocates pushed back fiercely.
They argued cash remained the dominant tool for criminal activity worldwide and warned against treating privacy technologies as inherently criminal because of isolated abuses.
The debate spread rapidly through legal, technological, and political circles.
Meanwhile, inside detention facilities across the United States, the accused customers arrested during Operation Closed Circuit awaited trial.
Some cooperated immediately.
Others denied everything despite overwhelming digital evidence.
A few appeared genuinely shocked to learn that real violence had occurred after their payments.
But prosecutors remained unmoved.
Under federal law, solicitation of murder-for-hire does not require successful completion of the requested act. The intent itself constitutes a serious felony offense.
And prosecutors intended to make examples of the defendants.
Internal Justice Department memoranda reportedly described the Final Order prosecutions as “strategically significant deterrence cases” designed to send a message about the traceability of dark web criminal behavior.
Whether that message would succeed remained uncertain.
Because the investigation revealed something deeply unsettling about the modern internet age:
People increasingly believe anonymity erases morality.
Behind encrypted networks and anonymous wallets, users who might never commit violence personally felt empowered to request it digitally, as though murder itself had become another online service transaction detached from physical consequence.
That illusion collapsed the moment FBI agents breached the basement door on Kelner Road.
But for some victims, the collapse came too late.
Rachel Engel is dead.
Three confirmed homicide victims are dead.
Multiple survivors continue rebuilding lives fractured by violence arranged through invisible networks they never knew existed.
And somewhere beyond the arrests, beyond the seized servers, beyond the courtroom battles still approaching, the unidentified perpetrators remain free.
Federal investigators continue tracing fragments of the missing $190,000 in Monero payments linked to actual attackers. International intelligence partnerships remain active. Additional indictments are expected. Sealed warrants continue circulating through federal courts.
Operation Closed Circuit did not end with the raid in Columbus.
It expanded.
Because investigators now believe Final Order may have intersected with broader underground ecosystems involving cyber fraud networks, ransomware laundering operations, and encrypted criminal marketplaces operating across Europe and Asia.
The basement server room in Ohio was never the entire system.
It was merely one visible node.
And perhaps the most chilling realization of all emerged during the FBI’s final internal after-action assessment.
For nearly three years, Final Order existed quietly beneath the surface of the internet, hidden behind layers of encryption and anonymity. Hundreds of people found it. Hundreds trusted it. Hundreds believed anonymous violence could be purchased safely from behind a screen.
Most were scammed.
Nineteen were not.
That ratio alone revealed the terrifying efficiency of the model. The operators did not need every contract to succeed. They needed only enough real violence to maintain credibility, fear, and demand.
In the end, the platform collapsed not because anonymity failed completely, but because human beings did what human beings always do eventually:
Someone made a mistake.
Seventy exposed seconds.
One unmasked IP address.
One suburban basement.
And suddenly the illusion of invisibility shattered beneath the weight of federal searchlights.
Yet even now, long after the servers stopped humming inside that house on Kelner Road, investigators acknowledge the deeper threat remains alive.
The technology still exists.
The marketplaces still evolve.
The demand still grows in the dark.
And somewhere tonight, another anonymous user may already be typing a name into another hidden website, believing no one will ever see it.
News
PART 2 San Diego DMV Examiner Sold 100+ Fraudulent Driver’s Licenses for $50,000+
San Diego DMV Examiner Sold 100+ Fraudulent Driver’s Licenses for $50,000+ . . . 🇺🇸 PART 2 — The Net Tightens: Surveillance, Stings, and the Collapse of a DMV Fraud Empire The Quiet Before the Storm For years, the fraud…
PART 2 Field Unit Enforced An Improper Household Perimeter Entry… Triggering A Massive $10M Resolution!
Field Unit Enforced An Improper Household Perimeter Entry… Triggering A Massive $10M Resolution! . . . 🇺🇸 PART 2: THE CANE THEY CALLED A WEAPON How a Disabled FBI Veteran Became the Target of a Routine Police Encounter That Ended…
PART 2 Racist School Staff Calls Cops on Black Mom Picking Up Her light skin Child—Unaware She’s the Mother
Racist School Staff Calls Cops on Black Mom Picking Up Her light skin Child—Unaware She’s the Mother . . .🇺🇸 PART 2: FROM A MOMENT OF PREJUDICE TO A MOVEMENT FOR JUSTICE What happened inside the brightly colored lobby of…
PART 2 Officer Attempted An Improper Commercial Facility Restriction… Challenging A Professional Attorney
Officer Attempted An Improper Commercial Facility Restriction… Challenging A Professional Attorney . . . 🇺🇸 PART 2: The Badge, the Camera, and the Cost of Power The courtroom was silent long before the judge entered. Not the ordinary silence of…
PART 2 California DMV Technician Indicted in Driver’s License Fraud Ring With 14 Others
California DMV Technician Indicted in Driver’s License Fraud Ring With 14 Others . . . 🇺🇸 PART 2: THE AFTERMATH — THE LICENSES THAT NEVER SHOULD HAVE EXISTED When federal agents placed handcuffs on Alfonso Casares that morning in Fresno,…
part 2 Texas Police Harass Federal Judge at Her Own Door — 8 Years in Prison Ends Their Careers
Texas Police Harass Federal Judge at Her Own Door — 8 Years in Prison Ends Their Careers . . . 🇺🇸 PART 2: The Hidden Network — How One False Arrest Uncovered a System Built on Fear, Power, and Silence…
End of content
No more pages to load