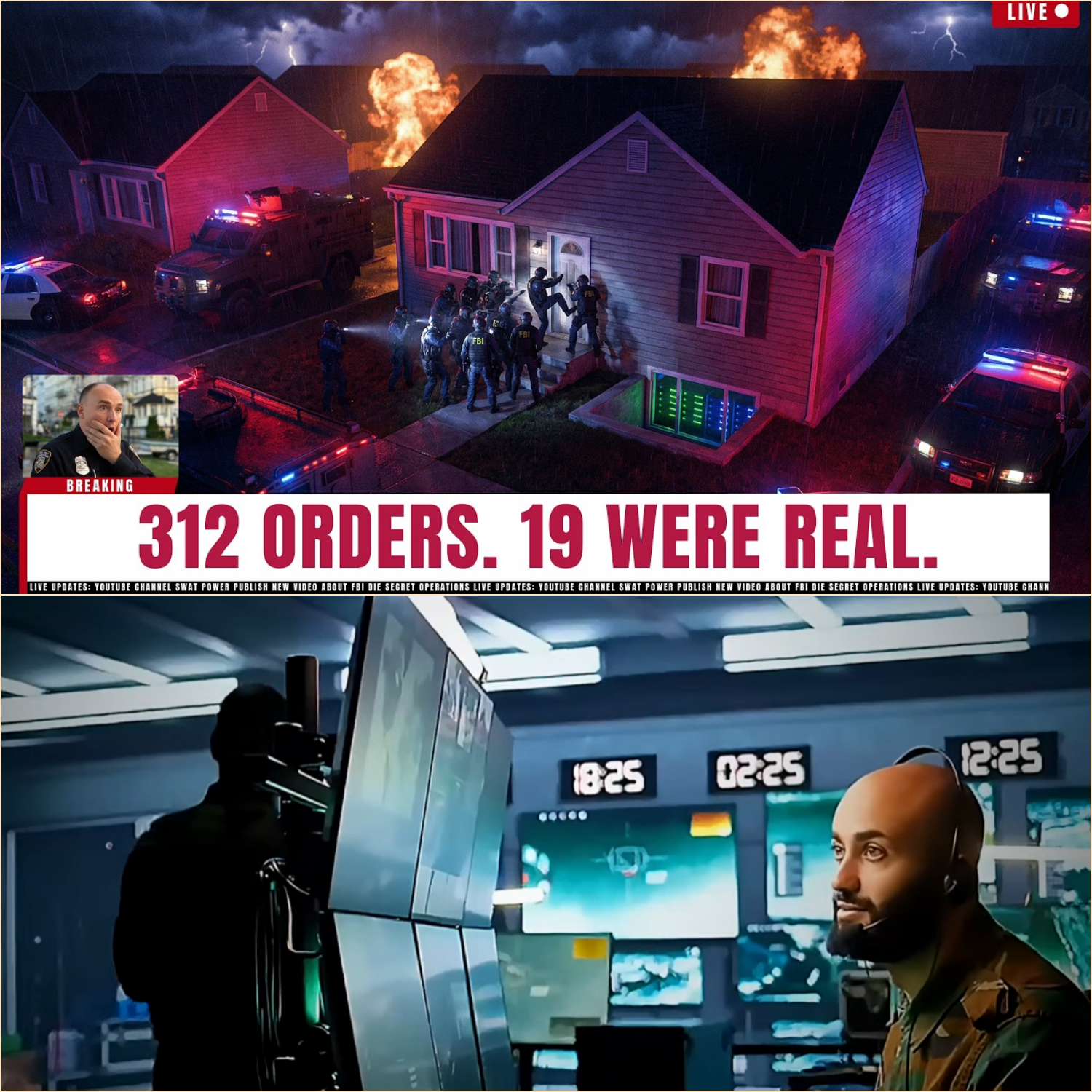
FBI CYBER UNIT TRACES Dark Web Hitman Service — 312 Orders, 19 Were Real
.
.
.
🇺🇸 FBI Cyber Unit Exposes “Final Order” Dark Web Hitman Network — 312 Murder Requests, 19 Turned Deadly
At 3:47 a.m. in Columbus, Ohio, the silence of an ordinary suburban street shattered beneath the weight of a federal operation years in the making. Twelve FBI agents in plain clothes surrounded a modest single-story rental house on Kelner Road. No flashing lights. No dramatic standoff. Just the cold precision of a raid designed to dismantle one of the darkest criminal marketplaces ever uncovered on the internet.
Inside the basement of the property, agents discovered six humming servers concealed behind soundproof panels. Sitting nearby on a foldout cot was 31-year-old IT contractor Marcus Drier, blinking into flashlight beams as federal agents stormed the room. What investigators uncovered on those servers would expose a sprawling dark web murder-for-hire operation known as “Final Order” — a hidden marketplace where people paid cryptocurrency to arrange real-world violence.
According to federal investigators, Final Order operated on the Tor network for nearly three years, offering anonymous users the ability to submit murder requests with chilling simplicity. Customers uploaded names, photographs, addresses, daily routines, and preferred timelines for attacks. Payments were accepted exclusively in Monero, a privacy-focused cryptocurrency designed specifically to obscure transactions and identities.
The site’s interface looked disturbingly professional. It featured customer support, FAQ sections, encrypted messaging systems, and even fake customer reviews crafted to build trust among users. A standard contract allegedly started at $5,000, while attacks involving public figures, gated communities, or security details carried significantly higher prices. “Rush orders” promised action within 72 hours for an additional fee.
For years, investigators believed the platform was mostly a scam — one of many fraudulent dark web operations exploiting violent fantasies for profit. In most cases, customers paid cryptocurrency, received fabricated confirmation messages, and never heard back again. The logic behind the scam was brutally simple: individuals attempting to hire killers were unlikely to report fraud to the police.
But beneath the deception lurked something far more dangerous.
Federal investigators later determined that of the 312 murder requests submitted through Final Order between 2023 and late 2025, at least 19 were connected to real-world acts of violence. Three cases resulted in confirmed homicides on U.S. soil. Others involved shootings, assaults, arson attacks, and attempted poisonings.
The breakthrough came after a homicide investigation in Norfolk, Virginia.
In January 2025, police discovered 34-year-old Rachel Engel dead inside her apartment from a single gunshot wound. There were no signs of forced entry, robbery, or obvious motive. Her estranged husband, Derek Engel, appeared untouchable. He possessed a verified alibi placing him at a corporate seminar in North Carolina during the killing.
Yet during a consent search of his laptop, detectives uncovered a Tor browser bookmark linked to Final Order and a trail of Monero payments totaling $7,500 routed through multiple anonymous wallets. The digital evidence was forwarded to the FBI Cyber Division. Within weeks, analysts confirmed the transactions matched known payment structures used by Final Order.
Suddenly, the case transformed from a local homicide investigation into a sprawling federal cyber operation codenamed “Operation Closed Circuit.”
The challenge facing investigators was immense. Final Order operated behind Tor’s layered anonymity protections. Payments moved through Monero, which unlike Bitcoin conceals wallet addresses and transaction values. Communications between customers and operators remained entirely internal to the platform. Traditional subpoenas and financial tracing methods proved nearly useless.
So the FBI adopted a dual strategy.
First, agents targeted customers whose requests appeared linked to real violence. Second, cyber analysts began painstakingly attacking the platform’s technical infrastructure itself, monitoring traffic patterns, server activity, hidden service descriptors, and metadata leaks across the Tor network.
For months, the operators made no mistakes.
Then came the error that destroyed everything.
On October 14, 2025, Final Order briefly went offline during what investigators later identified as a routine server migration. The outage lasted only 12 minutes. But during a catastrophic 70-second window, the newly configured server accidentally connected to the Tor network before its anonymity protections were fully activated.
For just over one minute, the platform exposed its real IP address.
That single mistake became the crack that federal investigators had been waiting for.
The IP address traced back to a residential Spectrum internet account in Columbus, Ohio, registered to Marcus Drier. Investigators immediately began covert surveillance. They monitored encrypted traffic patterns, documented suspicious server-related deliveries, and tracked unexplained cash deposits spread across multiple bank accounts.
The evidence mounted rapidly.
Agents observed massive encrypted data flows consistent with Tor hidden-service hosting. Financial investigators uncovered approximately $340,000 in structured cash deposits inconsistent with Drier’s freelance IT income. Packages containing rack-mounted batteries, networking hardware, and server components arrived regularly at the residence.
Meanwhile, Europol investigators identified another critical figure linked to the operation: 28-year-old Ukrainian national Arena Morozova, living in Kraków, Poland. According to investigators, Morozova allegedly managed Final Order’s customer communications, payment verification systems, fake reviews, and around-the-clock support operations.
Together, Drier and Morozova formed the operational core of the platform.
But the most chilling discovery emerged only after the FBI seized the servers.
Inside the database were 312 customer accounts containing payment records, target profiles, encrypted conversations, and completion codes tied to violent attacks. Investigators cross-referenced those records against unsolved assaults and homicides across the United States and Europe.
Nineteen cases aligned.
Three confirmed murders were directly connected to Final Order activity, including the killing of Rachel Engel. Other cases involved brutal assaults, arson attacks, and attempted poisonings. Federal prosecutors say the platform’s operators selectively connected the most persistent customers with actual perpetrators willing to carry out violence.
The platform’s scam operation had served as a filter — screening thousands of dollars from impulsive users while identifying serious customers prepared to follow through.
Even more alarming was the discovery of a hidden referral network buried within the platform’s architecture. Certain repeat users were allegedly offered commissions to recruit new customers in exchange for a percentage of future payments. Investigators described the structure as a limited but functional “multi-level criminal enterprise.”
By February 2026, Operation Closed Circuit had expanded into one of the largest coordinated cybercrime crackdowns in recent FBI history.
At exactly 5:00 a.m. Eastern Time on February 11, federal agents launched simultaneous raids across 11 states. Tactical teams arrested suspects ranging from disgruntled spouses to business owners, property managers, and software developers accused of soliciting violence through Final Order.
One suspect allegedly ordered an attack on a former business partner involved in a financial lawsuit. Another allegedly targeted a tenant who filed housing complaints. A software engineer in Atlanta allegedly attempted to hire attacks against both a former romantic partner and her new boyfriend.
Across the country, doors burst open simultaneously as federal teams raced to prevent evidence destruction and potential additional violence.
By sunrise, 13 suspects were already in custody.
A fourteenth suspect was captured days later at a motel in Reno, Nevada after attempting to flee across state lines.
Meanwhile in Poland, authorities arrested Arena Morozova under a European warrant tied to the operation.
The digital forensics phase that followed produced what FBI officials reportedly described as one of the most complete data recoveries ever obtained from a dark web criminal platform. Shockingly, much of the seized data was not encrypted at rest, exposing years of operational records.
Yet even after the takedown, major questions remain unanswered.
Investigators still have not identified the actual perpetrators responsible for carrying out the physical violence in the 19 confirmed attacks. Approximately $190,000 in Monero payments disappeared into anonymous wallets believed to belong to those attackers. Despite months of analysis, the individuals who pulled triggers, ignited fires, or carried out assaults remain unidentified.
That unresolved mystery continues to haunt investigators.
The Final Order case has fundamentally altered how federal agencies view dark web murder-for-hire platforms. For years, authorities considered most such websites elaborate scams with little operational capability. But Final Order demonstrated something more sinister: even a mostly fraudulent platform can still facilitate real killings when motivated users intersect with genuine violent actors.
Federal officials now warn that the infrastructure enabling Final Order still exists.
Tor remains operational. Privacy cryptocurrencies remain difficult to trace. Anonymous marketplaces continue evolving. And perhaps most disturbing of all, the demand persists.
Three people are dead.
Multiple others were assaulted or terrorized.
And 312 individuals, spread across multiple countries, believed anonymity could turn murder into a purchasable online service.
The servers seized from that quiet basement in Columbus may now sit locked inside an FBI evidence vault, but the darker reality exposed by Operation Closed Circuit cannot be boxed away so easily. Final Order was not merely a criminal website. It was a window into a hidden economy of grievance, obsession, revenge, and outsourced violence flourishing beneath the surface of the digital world.
The marketplace may be gone.
The infrastructure that made it possible is not.
Opening for Part 2
But the collapse of Final Order was only the beginning. As federal investigators dug deeper into the seized servers, encrypted chats, and hidden referral systems, they uncovered something even more terrifying — evidence suggesting the platform had connections to a wider underground network operating far beyond Columbus, Ohio. In Part 2, we follow the FBI’s hunt for the unidentified killers behind the 19 attacks, the secret crypto pipelines that funded them, and the chilling discovery that some of the platform’s most dangerous customers may still be free.
News
PART 2 San Diego DMV Examiner Sold 100+ Fraudulent Driver’s Licenses for $50,000+
San Diego DMV Examiner Sold 100+ Fraudulent Driver’s Licenses for $50,000+ . . . 🇺🇸 PART 2 — The Net Tightens: Surveillance, Stings, and the Collapse of a DMV Fraud Empire The Quiet Before the Storm For years, the fraud…
PART 2 Field Unit Enforced An Improper Household Perimeter Entry… Triggering A Massive $10M Resolution!
Field Unit Enforced An Improper Household Perimeter Entry… Triggering A Massive $10M Resolution! . . . 🇺🇸 PART 2: THE CANE THEY CALLED A WEAPON How a Disabled FBI Veteran Became the Target of a Routine Police Encounter That Ended…
PART 2 Racist School Staff Calls Cops on Black Mom Picking Up Her light skin Child—Unaware She’s the Mother
Racist School Staff Calls Cops on Black Mom Picking Up Her light skin Child—Unaware She’s the Mother . . .🇺🇸 PART 2: FROM A MOMENT OF PREJUDICE TO A MOVEMENT FOR JUSTICE What happened inside the brightly colored lobby of…
PART 2 Officer Attempted An Improper Commercial Facility Restriction… Challenging A Professional Attorney
Officer Attempted An Improper Commercial Facility Restriction… Challenging A Professional Attorney . . . 🇺🇸 PART 2: The Badge, the Camera, and the Cost of Power The courtroom was silent long before the judge entered. Not the ordinary silence of…
PART 2 California DMV Technician Indicted in Driver’s License Fraud Ring With 14 Others
California DMV Technician Indicted in Driver’s License Fraud Ring With 14 Others . . . 🇺🇸 PART 2: THE AFTERMATH — THE LICENSES THAT NEVER SHOULD HAVE EXISTED When federal agents placed handcuffs on Alfonso Casares that morning in Fresno,…
part 2 Texas Police Harass Federal Judge at Her Own Door — 8 Years in Prison Ends Their Careers
Texas Police Harass Federal Judge at Her Own Door — 8 Years in Prison Ends Their Careers . . . 🇺🇸 PART 2: The Hidden Network — How One False Arrest Uncovered a System Built on Fear, Power, and Silence…
End of content
No more pages to load