FBI Traps Boeing Engineer Selling F-35 Sensor Data — 14 Months of Wiretaps
.
.
.
FBI Traps Boeing Engineer in 14-Month Espionage Sting Involving F-35 Sensor Data
Everett, Washington — March 18, 2026
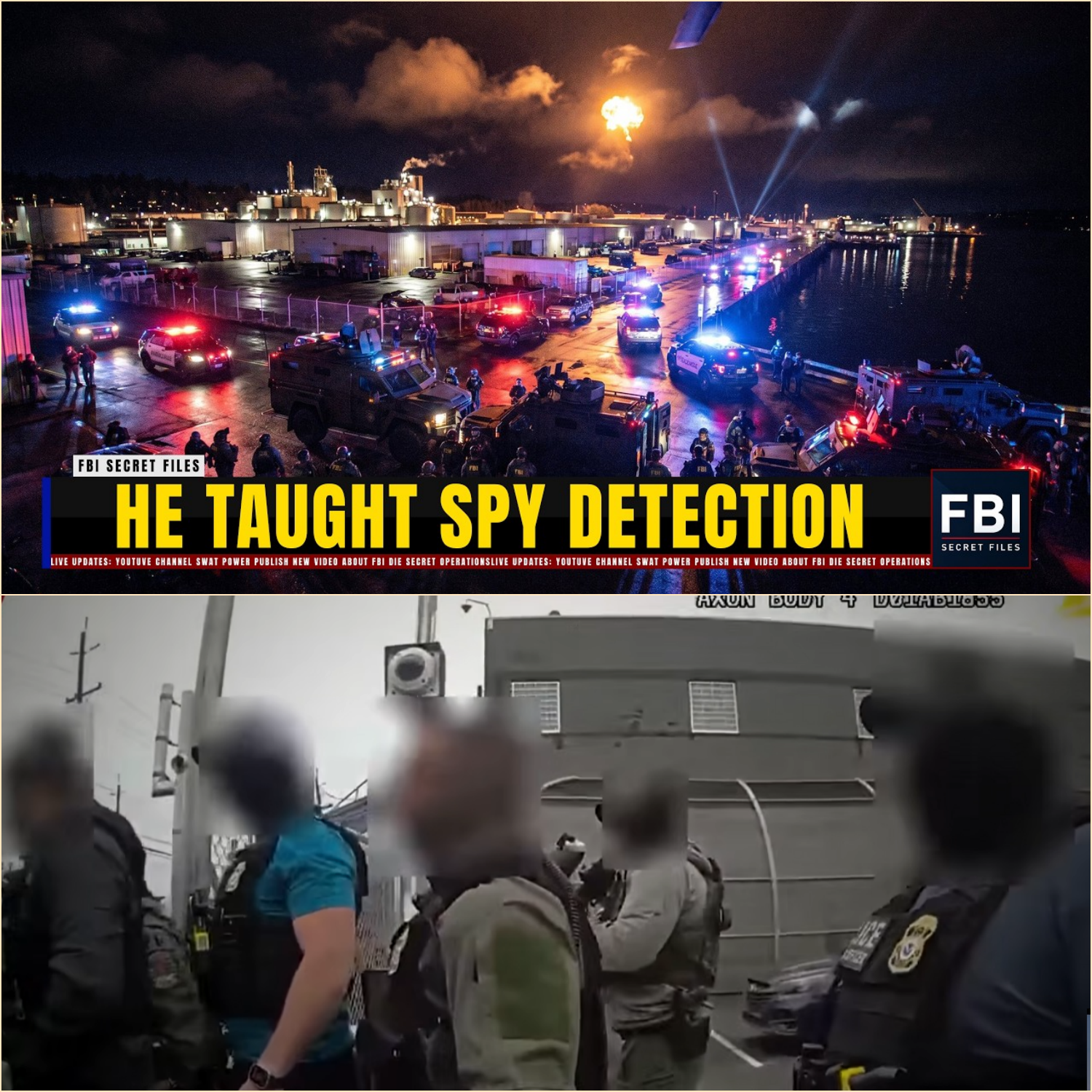
Before dawn broke over the fog-drenched industrial corridors north of Seattle, federal counterintelligence teams were already in motion. At 5:47 a.m., 41 agents moved in coordinated silence toward a Boeing-linked defense facility on Seaway Boulevard, executing the final phase of a classified 14-month investigation codenamed Lake View.
Inside a gray sedan parked on the second level of the employee garage sat Daniel Horac, a senior avionics systems engineer with nearly two decades of clearance history. He did not yet know that his routine morning arrival had been anticipated, mapped, and neutralized by one of the most extensive espionage surveillance operations conducted against a domestic defense contractor in recent years.
By 5:54 a.m., Horac was in federal custody.
What followed was the public unveiling of a case that investigators say exposed not just an insider threat—but a sophisticated foreign intelligence pipeline targeting the core sensor fusion systems of the F-35 Lightning II program.
A Quiet Arrest That Ended a 14-Month Counterintelligence Operation
According to court filings unsealed in federal court in Seattle, Horac allegedly transmitted sensitive defense data over a 14-month period to an unidentified foreign intelligence service. The material included classified components tied to next-generation avionics upgrades—specifically systems designed to integrate radar, infrared, and electronic warfare data into a unified battlefield picture.
Investigators described the case as one of the most deliberate insider operations they had seen in over a decade.
The arrest itself was quiet. No sirens. No announcement. Just a synchronized sweep across multiple access points inside and outside the facility.
By 6:30 a.m., the facility’s internal systems had been locked down.
The Man at the Center: A Trusted Engineer Turned Insider Threat
Horac, 45, was not a marginal contractor or temporary hire. He was a senior engineer embedded in a highly sensitive avionics program tied to sensor fusion architecture for advanced fighter systems.
He held a top-level clearance and had passed his most recent security reinvestigation in early 2025.
What made the case particularly striking, according to investigators, was Horac’s background. In 2019, he had participated in a counterintelligence awareness training program funded by defense security initiatives—training that specifically outlined the very surveillance and detection techniques later used against him.
One investigator described the irony bluntly in court documents:
“He didn’t just know the system. He taught parts of it.”
The First Digital Anomaly That Triggered the Case
The investigation did not begin with human suspicion. It began with metadata.
In October 2025, analysts at the National Security Agency flagged irregular timing patterns in encrypted communications traffic linked to a defense contractor network in Everett.
The content was not initially visible. What stood out was the structure—packet timing behavior consistent with previously documented foreign intelligence tradecraft.
That anomaly was referred to the Federal Bureau of Investigation counterintelligence division in Seattle.
Eleven days later, analysts identified a workstation tied directly to Horac.
The case quietly began.
A Slow-Build Espionage Operation
According to investigators, Horac’s alleged recruitment began in early 2024 during an academic conference in Vancouver, Canada, where he presented an unclassified technical paper on avionics integration challenges.
Two attendees later flagged in intelligence databases as foreign-linked researchers made contact.
From there, investigators say the operation evolved gradually.
Over the next several months, Horac traveled internationally multiple times, all properly disclosed through employer reporting systems. Nothing in those records was technically false.
But what the forms did not capture, prosecutors allege, was intent.
By late 2024, financial activity began shifting.
The Money Trail: Structured Payments and Hidden Cash Flow
Federal investigators identified approximately $340,000 in structured cash deposits spread across multiple states, deliberately kept below federal reporting thresholds.
Deposits were fragmented across credit unions in Washington, Oregon, and Idaho—each transaction designed to avoid triggering automated financial alerts.
One investigator described the pattern as “textbook structuring with intent awareness,” a violation of anti-money laundering statutes.
The payments allegedly corresponded with the transfer of sensitive defense data.
According to the indictment, Horac provided access to:
Infrared seeker calibration data for targeting systems
Sensor fusion algorithms used in real-time battlefield integration
Software architecture components linked to avionics upgrades
These systems are central to the operational capability of the F-35 Lightning II.
How the Data Was Allegedly Stolen
Rather than direct digital extraction, investigators say Horac used a low-tech method designed to evade automated monitoring systems.
He allegedly photographed classified terminal displays using a concealed device integrated into a modified water bottle. The images were then transferred to an encrypted secondary system stored in his vehicle.
From there, data was moved onto removable storage devices disguised as everyday maritime equipment.
The materials were allegedly passed via dead drops at a marina north of Everett, using devices disguised as boat key fobs.
Over 14 months, investigators documented 16 suspected exchanges.
The Breakthrough: A Marina, a Locker, and a Foreign Intelligence Link
A critical breakthrough came in February 2026 when surveillance captured Horac accessing a storage locker at Anacortes Marina.
Days later, a foreign national later identified in court filings as Chen Wei, allegedly associated with a foreign intelligence service, retrieved and deposited materials at the same location.
Investigators believe this exchange contained cryptocurrency credentials tied to payment flows.
While Chen Wei has not been extradited, prosecutors listed him as a co-conspirator.
The Undercover Operation That Exposed the Network
As surveillance intensified, investigators deployed undercover agents posing as junior defense contractors seeking consulting opportunities.
Within weeks, Horac allegedly began discussing recruitment of additional cleared employees.
According to recorded conversations, he described the effort as an “opportunity distribution network”—a term prosecutors interpret as internal talent penetration planning.
Three additional employees were identified as potential secondary targets.
None were charged in the initial indictment. Two later cooperated with investigators.
The Final Days Before Arrest
By mid-March 2026, investigators faced a narrowing window.
Encrypted communications suggested Horac may have suspected surveillance.
On March 17th, analysts detected a final transmission using the same timing-based encoding pattern that originally triggered the investigation.
The content remained unclear.
Fearing compromise of the operation, agents advanced the timeline by 12 hours.
The Arrest at Dawn
At 5:47 a.m. on March 18th, tactical teams moved simultaneously across two primary locations.
At the Everett facility, Horac was intercepted in the parking structure.
At a secondary storage site in Bellingham, agents executed a parallel warrant, uncovering:
12 laptops
47 encrypted storage devices
A custom-built offline encryption workstation
$64,000 in cash reserves
Simultaneous searches at his residence recovered handwritten logs detailing dead drop schedules and encrypted communications.
What Investigators Found Inside the System
Perhaps the most significant discovery was a handwritten operational log detailing 16 exchanges, including four that were previously unknown to investigators.
This suggested the existence of at least one additional, unidentified transfer location.
That aspect of the case remains unresolved.
Investigators have not publicly disclosed whether all transmitted data has been recovered or whether additional compromises exist within defense systems.
National Security Implications Remain Classified
While Horac has been charged with conspiracy to transmit national defense information, obstruction, and financial structuring offenses, the broader impact on weapons systems remains classified.
Officials have not confirmed whether operational modifications to F-35 systems will be required.
Nor have they disclosed whether other defense programs were affected.
What is known is that a formal damage assessment is ongoing between defense intelligence agencies and counterintelligence units.
Systemic Questions Raised by the Case
Beyond espionage, the investigation has raised uncomfortable institutional questions.
Horac passed his most recent clearance reinvestigation in 2025—months after alleged financial structuring and foreign contact activity had already begun.
One internal review cited in court filings noted that periodic clearance checks failed to detect behavioral and financial anomalies that later proved critical.
A senior investigator summarized the concern:
“The system worked exactly as designed. That’s the problem.”
The Larger Pattern: Insider Threats in High-Security Programs
Security analysts say the case reflects a broader trend: insider threats in high-value defense programs are increasingly difficult to detect using traditional vetting systems alone.
Unlike external cyberattacks, insider breaches exploit legitimate access, making detection dependent on subtle behavioral deviations rather than technical intrusion alerts.
The Lake View case, analysts say, combined both elements—behavioral intelligence failure and sophisticated counter-surveillance awareness by the suspect.
What Comes Next
Horac has pleaded not guilty.
A federal trial is scheduled for September 2026 in Seattle.
Prosecutors are expected to present 91 pages of affidavit material, including financial records, surveillance logs, intercepted communications, and forensic analysis of recovered devices.
Chen Wei remains outside U.S. jurisdiction.
The status of additional suspected recruitment targets remains under sealed proceedings.
An Unfinished Case With Closed Doors and Open Questions
Even as physical evidence has been seized and arrests executed, investigators acknowledge that not all aspects of the case are resolved.
The full extent of compromised data is still under classified review.
The identity of all recipients remains partially unverified.
And at least one suspected transfer location has not been definitively identified.
What began as a small timing anomaly in encrypted traffic evolved into a multi-agency counterintelligence operation spanning 14 months, multiple states, and international intelligence coordination.
And while one engineer is now in custody, investigators caution that the broader implications may not yet be fully understood.
As one federal agent noted in closing remarks:
“We closed the door on one case. We don’t yet know how many doors were opened.”
News
PART 2 San Diego DMV Examiner Sold 100+ Fraudulent Driver’s Licenses for $50,000+
San Diego DMV Examiner Sold 100+ Fraudulent Driver’s Licenses for $50,000+ . . . 🇺🇸 PART 2 — The Net Tightens: Surveillance, Stings, and the Collapse of a DMV Fraud Empire The Quiet Before the Storm For years, the fraud…
PART 2 Field Unit Enforced An Improper Household Perimeter Entry… Triggering A Massive $10M Resolution!
Field Unit Enforced An Improper Household Perimeter Entry… Triggering A Massive $10M Resolution! . . . 🇺🇸 PART 2: THE CANE THEY CALLED A WEAPON How a Disabled FBI Veteran Became the Target of a Routine Police Encounter That Ended…
PART 2 Racist School Staff Calls Cops on Black Mom Picking Up Her light skin Child—Unaware She’s the Mother
Racist School Staff Calls Cops on Black Mom Picking Up Her light skin Child—Unaware She’s the Mother . . .🇺🇸 PART 2: FROM A MOMENT OF PREJUDICE TO A MOVEMENT FOR JUSTICE What happened inside the brightly colored lobby of…
PART 2 Officer Attempted An Improper Commercial Facility Restriction… Challenging A Professional Attorney
Officer Attempted An Improper Commercial Facility Restriction… Challenging A Professional Attorney . . . 🇺🇸 PART 2: The Badge, the Camera, and the Cost of Power The courtroom was silent long before the judge entered. Not the ordinary silence of…
PART 2 California DMV Technician Indicted in Driver’s License Fraud Ring With 14 Others
California DMV Technician Indicted in Driver’s License Fraud Ring With 14 Others . . . 🇺🇸 PART 2: THE AFTERMATH — THE LICENSES THAT NEVER SHOULD HAVE EXISTED When federal agents placed handcuffs on Alfonso Casares that morning in Fresno,…
part 2 Texas Police Harass Federal Judge at Her Own Door — 8 Years in Prison Ends Their Careers
Texas Police Harass Federal Judge at Her Own Door — 8 Years in Prison Ends Their Careers . . . 🇺🇸 PART 2: The Hidden Network — How One False Arrest Uncovered a System Built on Fear, Power, and Silence…
End of content
No more pages to load